Stealth
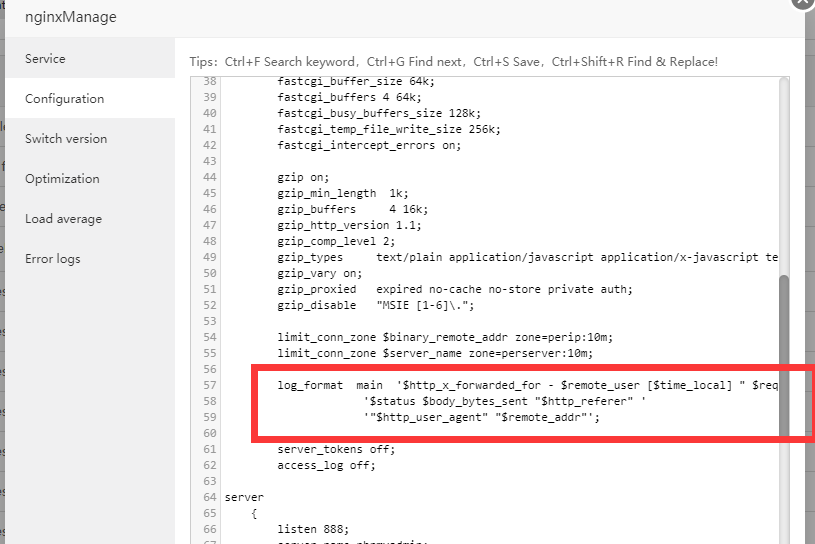
If you use nginx, you can try to add this log configuration in the nginx manager to record the customer's real access address
log_format main '$http_x_forwarded_for - $remote_user [$time_local] " $request" '
'$status $body_bytes_sent "$http_referer" '
'"$http_user_agent" "$remote_addr"';
Add mainafter the log path of the website where you need to modify the log format
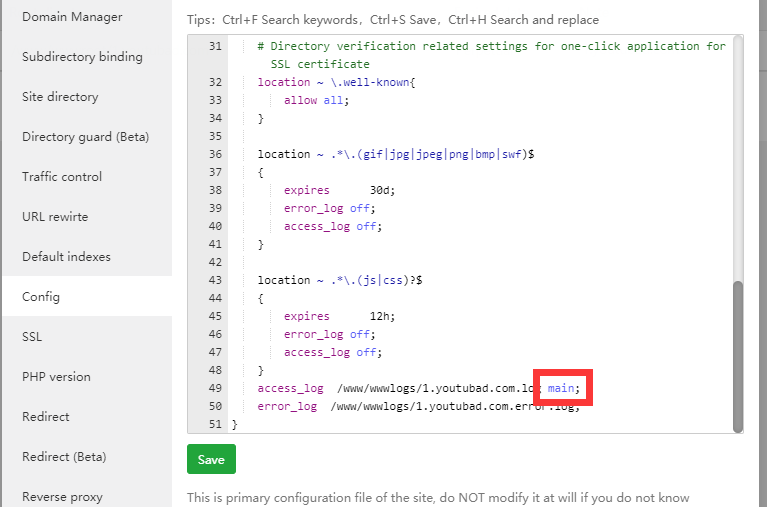
This way your fail2ban can accurately intercept the IP